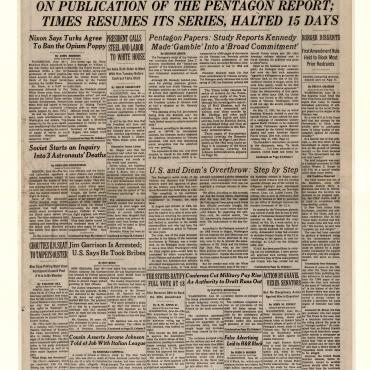
2013: Snowden Spills Government Secrets
Does the First Amendment protect the leaking and publication of classified information?
Get even more great free content!
This content contains copyrighted material that requires a free NewseumED account.
Registration is fast, easy, and comes with 100% free access to our vast collection of videos, artifacts, interactive content, and more.
NewseumED is provided as a free educational resource and contains copyrighted material. Registration is required for full access. Signing up is simple and free.
With a free NewseumED account, you can:
- Watch timely and informative videos
- Access expertly crafted lesson plans
- Download an array of classroom resources
- and much more!
This Critical Debate is part of a Debate Comparison:
See all Debate Comparisons- Constitution
- Journalism
- National Security
- 9-12
- College/University

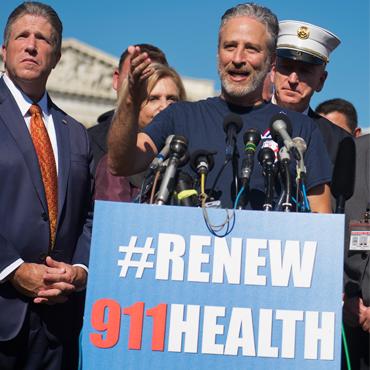
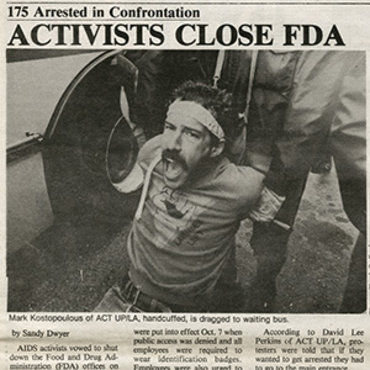
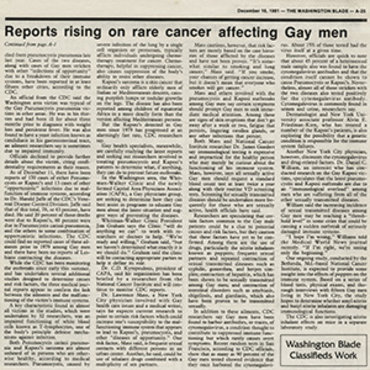
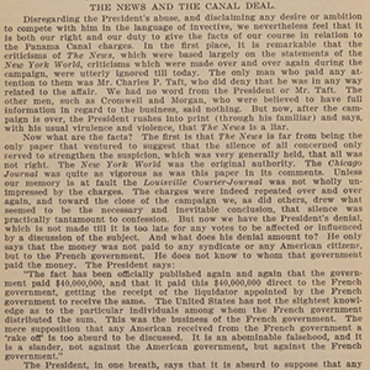
Reporter Glenn Greenwald, who published stories based on classified information provided by Edward Snowden, speaks with the press in Hong Kong.
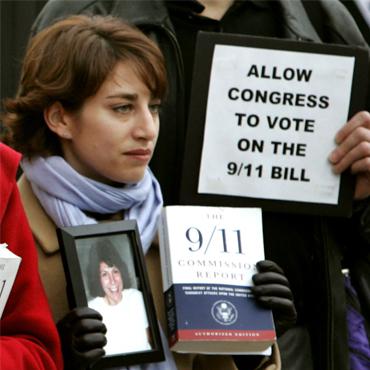
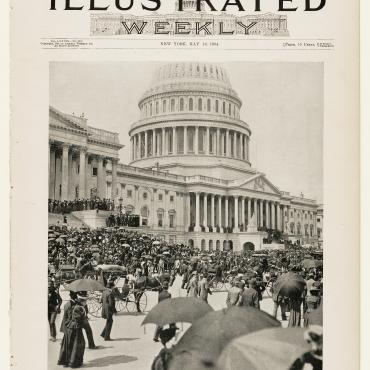
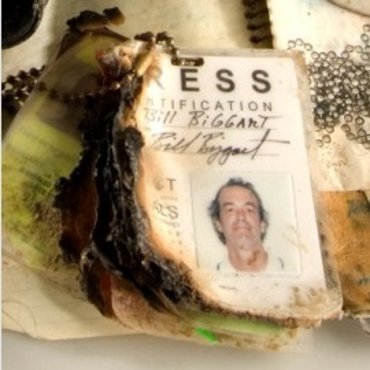
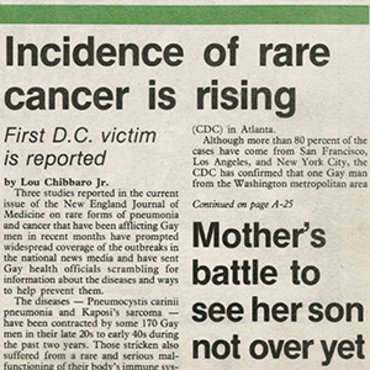
Looking Back: 9/11 Connections
Use the artifact viewer to explore the image below and discuss the following questions:
- What happened/is happening in this image? What story does it tell?
- How is this image connected to the events of Sept. 11, 2001?
- How could you use this image to make an argument about the state of freedom in the U.S.? About national security?
What would you do if you discovered secret government programs that monitor Americans' phone calls and emails?
You are an analyst working as a contractor for the National Security Agency. Using the access your job provides, you discover classified documents relating to multiple government surveillance programs. One program allows the NSA to directly access information from the servers of Microsoft, Google and other major tech companies. Another program collects the phone records of millions of Americans directly from a major communications company. Although this is legal under legislation passed after the 9/11 attacks, these programs go far beyond what most Americans believe the government to be doing.
Accessing and sharing these documents could get you in serious legal trouble. You might even be charged with treason.
What do you do?
-
Create a website and publish the information you’ve found online.
The public deserves to know immediately that the U.S. government is spying on their communications.
-
Find a journalist who is willing to write a story about the information you’ve found.
Going through the press will reach a larger audience and ensure the story’s credibility.
-
Don’t reveal the information.
You could get in serious legal trouble, and the programs help catch terrorists.
-
Something else.
Explain.
- Should the First Amendment protect leaking classified information? What about publishing information someone else leaked?
- What could be the consequences – for you and for other people – of sharing this information? How will citizens react? Lawmakers? The media?
- How could revealing these programs affect national security?
- If you choose to seek out a journalist, would you want to remain an anonymous source?
- Why did the government create these programs? Why do some argue they go too far?
Have students use the Analyzing Evidence and Making Your Argument handouts to collect and organize additional information about the case, then form an argument supported by evidence. Give groups 30 minutes to prepare, or assign as homework. (Note: Students may wish to organize their sources and evidence using a spreadsheet, such as Google Sheets.)
-
Common Core State Standards: CCSS.ELA-LITERACY.CCRA.L.3
Apply knowledge of language to understand how language functions in different contexts, to make effective choices for meaning or style, and to comprehend more fully when reading or listening. -
Common Core State Standards: CCSS.ELA-LITERACY.CCRA.L.4
Determine or clarify the meaning of unknown and multiple-meaning words and phrases by using context clues, analyzing meaningful word parts, and consulting general and specialized reference materials, as appropriate.
-
NCSS C3 Framework: D4.1.6-8 and D4.1.9-12
6 - 8: Construct arguments using claims and evidence from multiple sources, while acknowledging the strengths and limitations of the arguments. 9 - 12: Construct arguments using precise and knowledgeable claims, with evidence from multiple sources, while acknowledging counterclaims and evidentiary weaknesses.
-
ISTE: 7d. Global Collaborator
Students explore local and global issues and use collaborative technologies to investigate solutions.
-
National Center for History in the Schools: NCHS.US History.Era 10
Standard 1: Recent developments in foreign policy and domestic politics Standard 2: Economic, social, and cultural developments in contemporary United States
-
Center for Civic Education: CCE.III
A. How are power and responsibility distributed, shared, and limited in the government established by the United States Constitution? D. What is the place of law in the American constitutional system? E. How does the American political system provide for choice and opportunities for participation?